Side-Channel Attacks: Langer EM Probes and CPA
Evaluation and comparison of various Langer EM probes for CPA-based side-channel attacks and cryptographic key extraction
March 2, 2026
Side-Channel Attacks: Langer EM Probes and CPA
In hardware security research, side-channel attacks play a central role – unlike traditional software attacks, they use physical measurements to extract sensitive data. The goal is to measure the “whisper” of the chip and then extract secrets using various analysis methods.
In addition to power consumption measurements, electromagnetic probes (EM probes) are among the most important tools for capturing chip emissions and uncovering vulnerabilities in cryptographic implementations. This article shows how an evaluation with EM probes works, what insights it provides, and why it is essential for security assessment.
Various probes from Langer EMV-Technik are compared with their characteristics for a non-hardened target. Langer EMV-Technik is an established manufacturer of probes and tools for measuring electromagnetic fields. The primary goal is to use the insights gained from the evaluation to perform a quick assessment of a test device, which can be used in practice as a simple test for the disclosure of secrets.
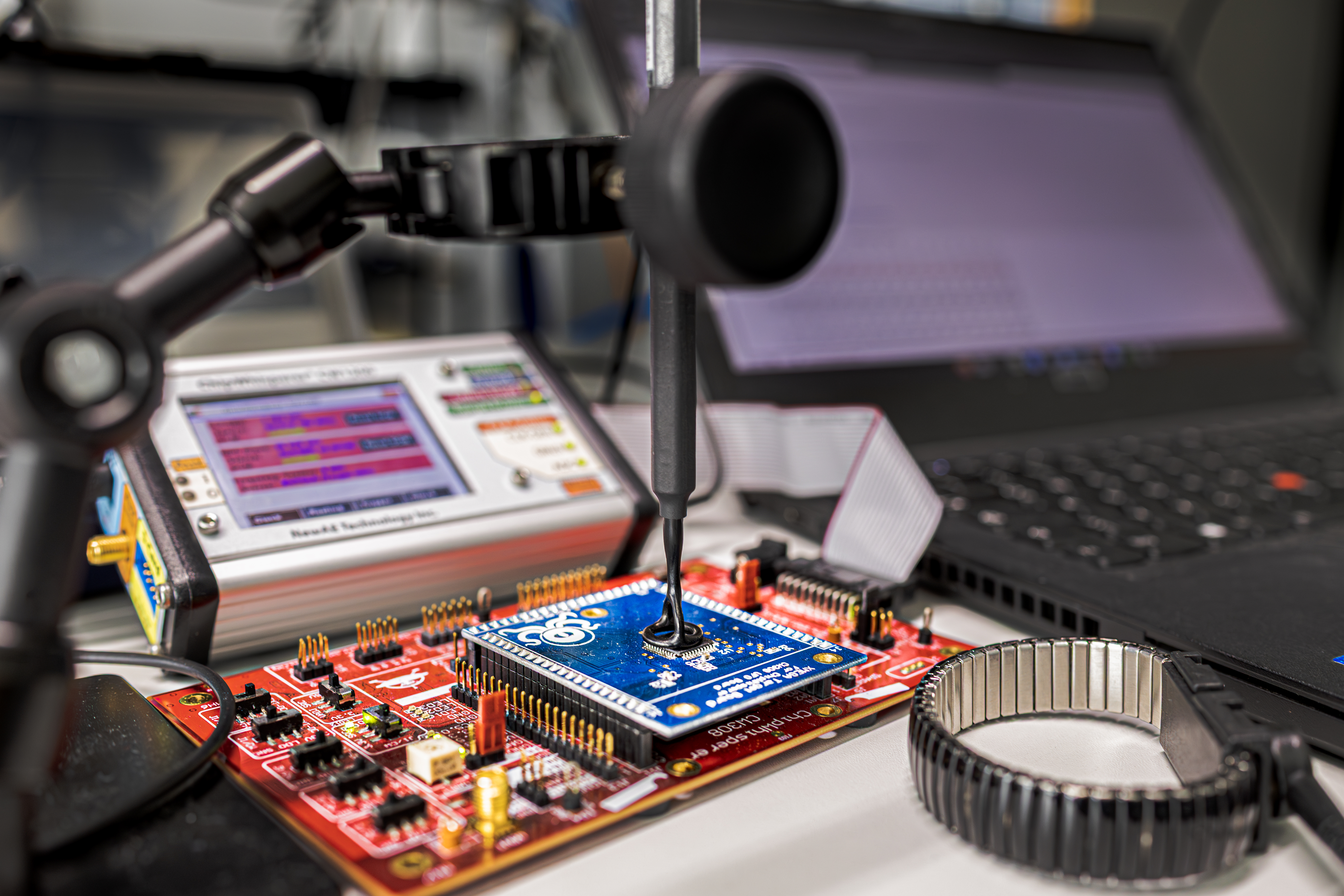
The evaluation focused on the use of various near-field probes and a preamplifier from Langer EMV-Technik. A Correlation Power Analysis (CPA) – a statistical method for extracting cryptographic keys – was performed using ChipWhisperer®. An ATxmega128D4 microcontroller (128 KB Flash, 32 MHz, 8-bit) served as the test target, as used in many simple consumer devices. The target was deliberately not hardened to obtain the simplest possible setup for comparability of measurement results.
Experimental Setup and Procedure
The test setup consists of the following components:
- Langer EMV-Technik Near-field probes RF 30 MHz - 3 GHz:
- Langer EMV-Technik Preamplifier PA 306 SMA set for signal amplification
- ChipWhisperer® CW1200 (oscilloscope/recording device)
- ChipWhisperer® CW308 UFO Board (adapter)
- CW308T‑XMEGA Target Board (target device)
- Target Device: ATXmega128D4-AU
- 128 KB Flash Memory
- Clock Speed: 32 MHz
- Target Architecture: 8-bit Harvard
- Supply voltage 3.3 V
- Target Device: ATXmega128D4-AU
The goal was to successfully perform a Correlation Power Analysis (CPA) with the three different H-field probes (RF-B 0_3-3, RF-B 3-2, RF-B 50-1), with different coil diameters and a preamplifier PA 306 SMA using the ChipWhisperer® stack (CW1200, CW308 UFO, CW308T-XMEGA Target), record measurement data, and compare them. The notebook H-Field Probe Demo 1 (with CPA) .ipynb available in the ChipWhisperer Jupyter GitHub was used for this purpose. The preamplifier has a gain of 30 dB and operates in a frequency range from 100 kHz to 6 GHz. It is therefore very well suited for the target used here with a clock frequency of 32 MHz. In particular, the use of different sized probes was to be evaluated with regard to application on a target with a closed package (plastic housing) and manual placement on the target.

The idea behind this was to find out how easy it is to manually place a probe on an unknown test device and read the key from the chip. The orthogonal position of the coil to the probe body facilitates positioning.
For each of the three H-field probes, the CPA script was executed to realize the side-channel attack. The measurements were recorded via the ChipWhisperer® to enable synchronous sampling to the processor clock. The number of traces required was kept as low as possible, with a constant 5,000 samples recorded in each case. With a sample duration of approximately 33.85 ns, the ADC resolution is 10 bits.
For best results, the probes were placed vertically and as close as possible to the target. Placement was done manually with a probe holder and adjusted based on results from the t-test procedure to find a good position. The setup was not additionally shielded.
Results
With all tested probes, it was possible to successfully achieve key extraction using the CPA method, with CPA showing statistical significance of the results in all measurement series performed. The respective probes required the following number of traces (see Diagrams 1-3):
- RF-B 0_3-3: 550 traces
- RF-B 3-2: 250 traces
- RF-B 50-1: 100 traces
Diagram 1: Correlation progress for Byte 0 with RF-B 0.3-3

Diagram 2: Correlation progress for Byte 0 with RF-B 3-2

Diagram 3: Correlation progress for Byte 0 with RF-B 50-1

The statistical significance can be read from the diagrams for byte 0 as an example. The thick red line represents the correlation of the correct key byte. As soon as this value is significantly above the correlations of the other values, the minimum number of traces for a reliable statement has been reached.
It can be seen that the number of necessary traces decreases with the size of the measurement radius. This is because a larger measurement range provides greater tolerance for manual placement, and the probe does not need to be positioned exactly at the optimal position on the target. It is expected that automated positioning with the smaller probes, especially with weaker signals, could deliver better results. The larger measurement radius also increases the recorded noise, but the Langer EMV-Technik probes have a very good signal-to-noise ratio, which compensates for this.
For comparison, the attack – measured via a shunt resistor in the same target’s power supply – requires approximately 100 traces, as there is a very strong signal here, and with the EM probe with preamplifier included with the ChipWhisperer approximately 250 traces. However, measurement via a shunt resistor is very difficult in practice, as in many cases there are multiple power supplies and capacitances in the system and hardware manipulation is often required. Therefore, in these cases it is much easier to place a probe over the target. Since this was a non-hardened target, the signal could already be detected well using an oscilloscope.
Conclusion
The following insights can be derived from the results:
- The hardware stack used (CW1200, CW308 UFO, Target Board) provided a reliable platform for evaluating side-channel analyses.
- The combination of Langer EMV-Technik near-field probes and preamplifier proved to be extremely functional and was crucial for the success of the attacks.
- The attack can be performed after simple manual adjustment of the setup.
- Transferability to hardened or faster operating targets is feasible, and the probes can therefore be used for quick verification of side-channel leaks.
- The Jupyter Notebook provided by ChipWhisperer® enabled a simple option to evaluate the performance of CPA analysis on the XMEGA target.
- Despite different probe designs, CPA was very reliable with all probes. It was not necessary to perform automated and time-consuming testing of the exact placement of the probes.
- Large probes are suitable for quick identification of side-channel leaks, especially with closed packages, as there is greater tolerance for placement.
- It can be assumed that smaller probes can be used better against hardened targets and through exact placement, and offer higher precision especially with greater interference. Further tests are required for this.
The use of larger probes can be used for quick analysis in combination with a good signal-to-noise ratio and little prior knowledge. With smaller probes, there is also the possibility of covering many advanced requirements. The simple handling, especially through the possibility of vertical placement of the probe, is also an advantage when mechanical automatic placement is to be used.